AIM – Access and identity management
What is AIM?
AIM stands for Advanced Identity Management – a comprehensive PIAM system that centralizes your processes for physical and digital identity management. It connects all access control systems and workplace management solutions, automates approval processes and synchronizes data in a user-friendly interface. Whether onboarding new employees, granting secure access or managing authorizations for visitors and external companies – AIM simplifies and optimizes the management of your access control.
Central identity management
AIM connects all your access control systems in a central platform that allows you to manage identities and authorizations for employees, suppliers and visitors easily and efficiently. It improves your existing access infrastructure and enables organizations to standardize, centrally control or unify their access policies globally – without having to replace existing hardware.
Seamless integration into existing security systems
AIM connects your existing security infrastructure, such as access control, video surveillance and alarm systems, in a central platform. This gives you a clear overview and allows you to manage security more efficiently.
Role-based access control
With AIM, you can define role-based authorizations that precisely regulate who can access certain areas or resources. This increases security, as users only receive the access rights they need for their role. The same applies to operators: they only see and edit the data that corresponds to their respective role.
Automated workflows and real-time monitoring
AIM simplifies processes such as access requests, approvals, recertifications and event monitoring with automated workflows. Real-time alerts inform you of unusual activity and detailed reports support you with audits and compliance
Scalable for companies of any size
Whether you manage a single site or a global organization, AIM adapts to your growth. The solution is flexible and can be adapted to any industry and any location, making it a future-proof investment in security.
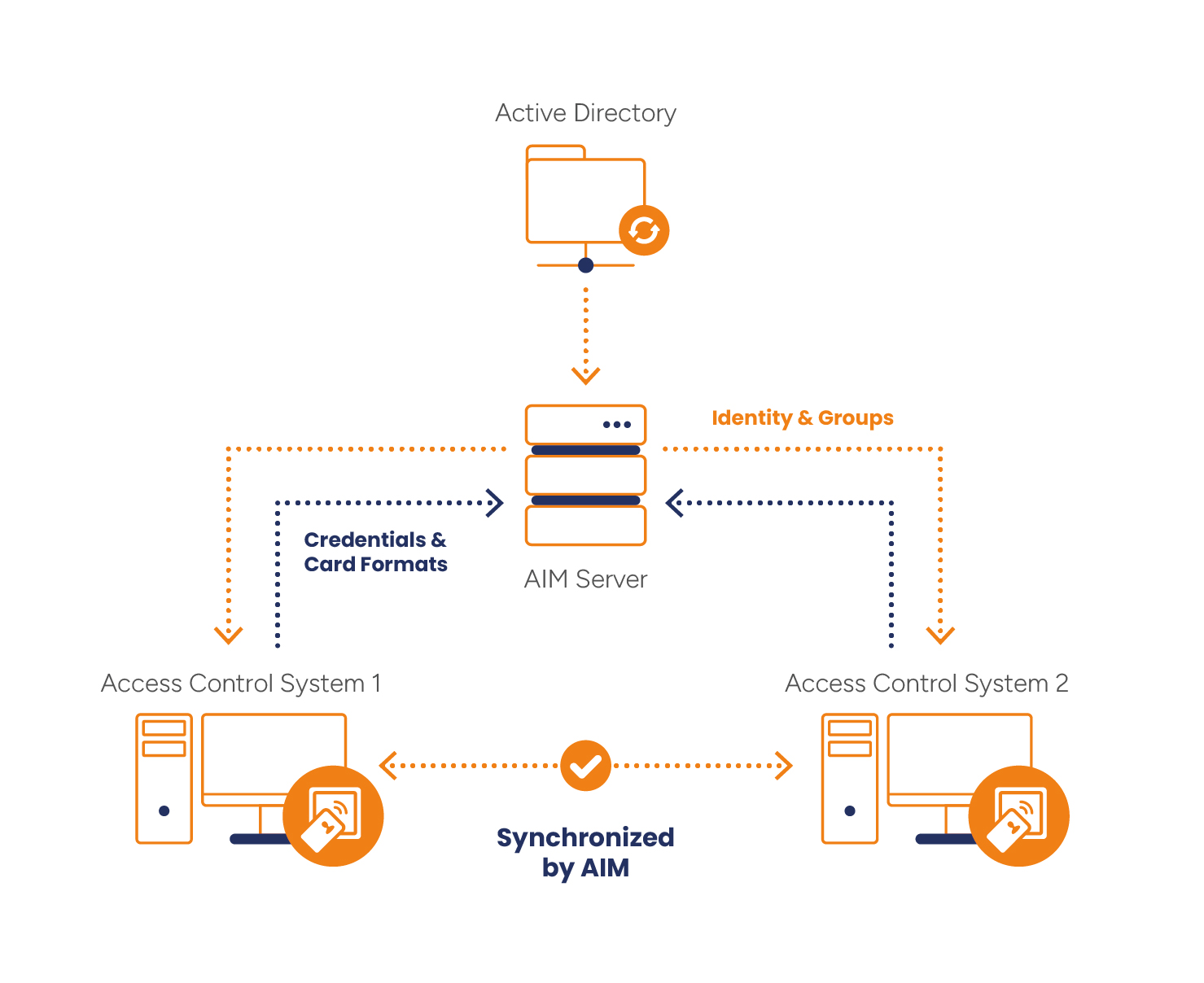
How does AIM work?
- Identities (cardholders/users) and group rights are taken from a leading data source – in this example from the Active Directory.
- Credentials (card information and formats) are synchronized between all access control systems.
PIAM
Why are PIAM solutions essential for modern companies?
In today’s business world, digital and physical identity and access management (PIAM) is essential. With the increasing complexity of organizations and growing security risk, both internally and externally, PIAM solutions such as AIM:
Uniform guidelines
Creation of on-boarding and off-boarding procedures and standardization of the login procedure for the management of login data.
Improved security
Prevent unauthorized access with extended role-based permissions.
More efficient business processes
Automate time-consuming tasks such as access approvals and security reports.
Better resource management
Manage employee, contractor and visitor access on a single platform to increase data accuracy and reduce administrative overhead.
Conformity
Ensure that your company complies with industry regulations and produces appropriate reports and documentation.
Flexible integration
AIM supports open protocols such as PLAI, a RESTful API and proprietary interfaces for connecting access control systems, biometrics and other identity and visitor management systems from different manufacturers. Our portfolio of supported systems is growing continuously and is constantly being expanded with new developments.
















Access control / security management systems
AIM ensures the synchronization of logical and physical access rights according to employee roles and enables the seamless management of identities and authorizations. With AIM, companies benefit from increased security, simplified administration and the ability to continue using existing access control infrastructures efficiently.
Manufacturer |
System |
| AMAG | Symmetry |
| Brivo | Brivo Access |
| Gallagher Security | Command Centre |
| Genetec | Security Center |
| HID | HID Origo |
| Honeywell | ProWatch |
| Inner Range | Integriti |
| Interflex | IF-6040 |
| Johnson Controls (JCI) | P2000 |
| Kantech | EntraPass |
| Kastle | Identity Connect |
| Lenel | OnGuard |
| Microsoft | Active Directory |
| Microsoft | Entra ID |
| Millenium | Millenium Ultra |
| Nedap | AEOS |
| Salto | Salto KS |
| Siemens | SiPass |
| Software House | C-Cure 9000 |
| Synguard | Synguard |
AIM license model
Included in every license
- Web user interface
- Monitoring the system environment
- Cardholder management

Express
Up to 3 adapters and max. 3,000 users
Basic
Up to 5 adapters and max. 5,000 users

Professional
Up to 10 adapters and max. 25,000 users

Enterprise
Unlimited number of adapters and users